Alan Berg
I am an author and consult about Analytics, IT automation, Quality… Meer over Alan Berg
The LSAC 2018 hackathon attacking Learning Analytic research questions took place in Amsterdam on October 24th and 25th as a post workshop of the LSAC2018 conference. The theme of the conference was ‘Deploying Artificial Intelligence to Improve Learning while Ensuring Privacy’. Three teams worked on emerging issues in the field.
We addressed Four themes:
Each time we help organize a hackathon on the subject of Learning Analytics we the organiser’s try to add an additional optimisation. In this hackathon we added a message to the GitHub evidence hub trying to make it easier for the next hackathon to build on top of previous hackathons. We also added an evening dinner which enabled a lot of ad-hoc sharing of ideas.
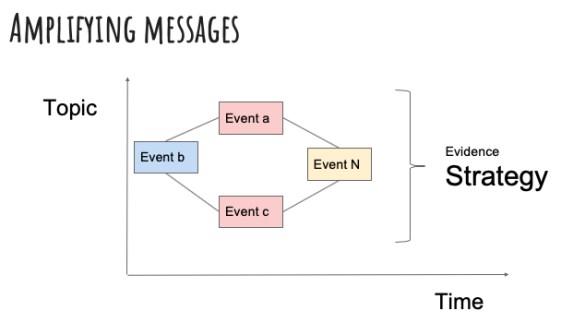
In the past I have been involved in a considerable number of successful hackathons, however, we have not always planned for success. We were looking for a strategy to amplify the value of the productive efforts. Interconnection and consistency are the obvious and fruitful strategies.
This GitHub location is the evidence hub for the LSAC 2018 hackathon. A two-day event for hacking anonymous Educational data and infrastructure for the benefit of the lifelong learner.
For information on a series of interrelated hackathons please visit the website. Note that currently a hackathon is planned for both LAK19 and for LSAC2019 which will be held in Nance in France.
If you wish to plan your own event. You are more than welcome to make contact and compare notes (a.m.berg AT uva.nl)
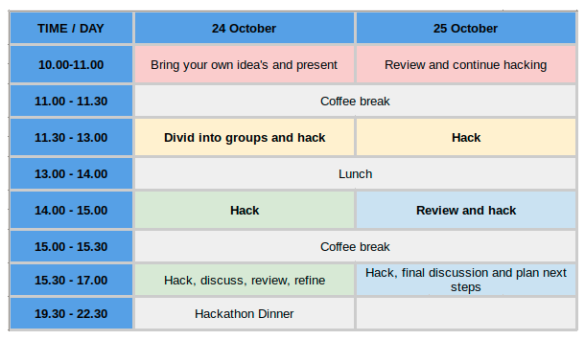
The Agenda was:
The hackathon isn’t a conventional academic workshop. New ideas are still encouraged and very welcome on the day. One key difference to a normal workshop is that we expect to produce outputs during the workshop, as well as having inputs at the start of the hackathon. Hackathon attendees can get themselves added to the Participants Team to get write access.
We followed the practice of previous hackathons, taking care to organise and preserve the outputs from the hackathon in GitHub. This repository has been set up for the 2018 hackathon; this included:
Directories in Github and their meaning:
The default outbound software license for the evidence stored in this Github repository is the Apache License, Version 2.0. In the absence of an explicit licensing declaration, software evidence is implicitly licensed under the Apache License, Version 2.0. More specific information about the Apache License is available in the Apache License and Distribution FAQ.
This is the message the event passes on to the next event.
We addressed Four themes:
An experiment around neural networks to classify successful and unsuccessful CPR training events took place. Neural networks are a natural match to the problem space.
We concluded that we should provide more opportunities for student participation. There is an on-going debate around how to provide a motivating reward system.
The review was merged with the SURF activity around their next generation experimental National infrastructure
Initial Presentation and Lessons learned
The dashboard took shape, however much work is required. Consider taking further:
All in all, an enjoyable and productive and soon to be interconnected event.
Well done participants.
Until the next time.
I am an author and consult about Analytics, IT automation, Quality… Meer over Alan Berg

0 Praat mee